Use the Clues
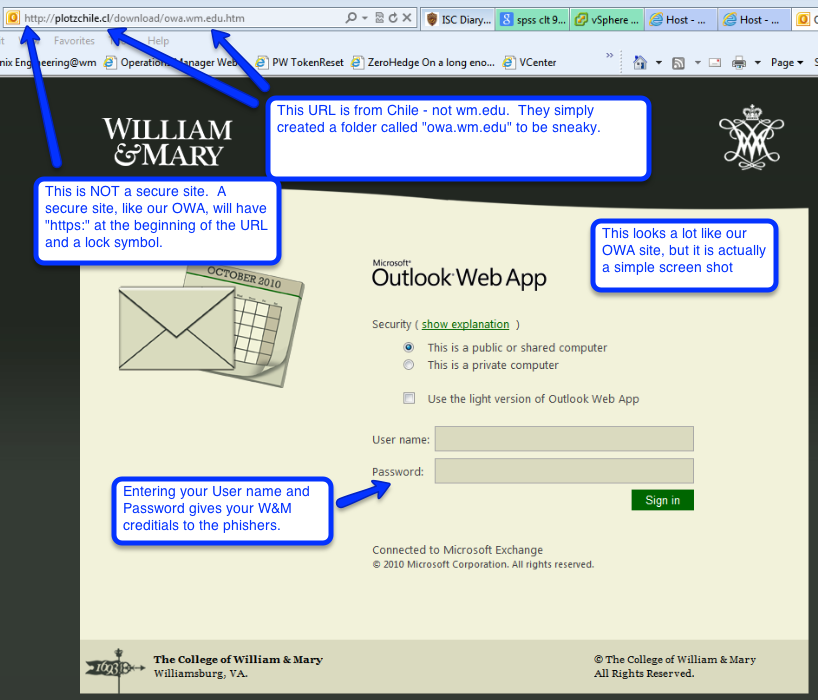
 We are experiencing yet another phishing attack. This one is particularly slick as it imitates our OWA login screen and steals your W&M credentials when you try to "Log In" to it.
We are experiencing yet another phishing attack. This one is particularly slick as it imitates our OWA login screen and steals your W&M credentials when you try to "Log In" to it.
When accounts are compromised, they turn into spam-bots, blasting out thousands of pieces of spam in just a few minutes. The accounts are quickly disabled by W&M engineers to stem the flow of spam, forcing the account owners to contact IT to get their accounts restored. When spam gets really bad, we (W&M) get blacklisted from email servers all over the world. Our out-going email comes to a standstill. Nobody wants this to happen.
Finding Clues
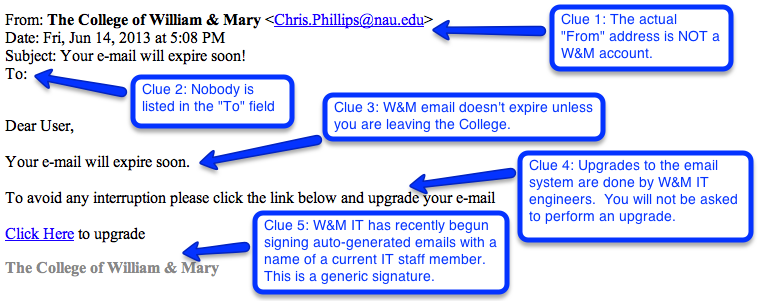
As phishing emails become more sophisticated, we ALL must be more vigilant in detecting them. Here are ways to identify a phishing email:
- Misspellings and Grammar Mistakes– There will often be misspelling and/or grammatical errors in the body of the email and/or subject line
- Who is it from? – Click on the "From" address to make sure the email is coming from a W&M account (Simply reading the address line can be deceiving)
- Login Pages - If asked to go to a page to login, make sure the URL of that web page is from W&M. (Ex. https://example.wm.edu or www.wm.edu/example)
- Weekend/Holidays – Phishing attacks will often strike on weekends and holidays when they know the IT offices are closed.
Take a look at this phishing attempt. Even though it is pretty convincing there are several clues that indicate that something isn't right.
Prevention is the Key
- DO NOT respond to an email asking for your password. W&M IT will never ask you to do this.
- We will publicize any major IT events in the W&M Digest, Student Happenings, and in the Announcements section of the W&M IT website. We don't do any major move, upgrades or maintenance without prior warning.
- W&M IT will no longer ask you to sign into pages directly from an email link.* We will direct you to the W&M IT website first where you can find a link for the service. Expect this for the annual change of password, to verify your phone location verification, and the annual device authentication.
Act Quickly!
If in doubt, forward the email in question to [[support]] for verification. This account is heavily monitored. If you identify a phishing email, forward it immediately to [[abuse]]. The quicker a phish is reported, the quicker IT Engineers can act to quarantine it.
If you responded, or suspect you responded, to a phishing email, reset your password immediately!
 Skip to main content
Skip to main content
